On November 22, 2021, the popular web hosting provider GoDaddy announced that an unauthorized third party accessed their Managed WordPress hosting environment. Beginning on September 6, 2021, the unauthorized third party accessed the email address and customer number of 1.2 million active and inactive Managed WordPress customers. Additionally, the original WordPress Administrator password for each instance and the sFTP and database usernames and passwords were also exposed. Furthermore, a subset of active customers had their SSL private key exposed.
The scope of the security incident allows for potential phishing attacks against past and present customers, may have permitted Administrator access to WordPress sites, and allowed for possible access to files and the WordPress database. For the subset of active customers whose SSL private key was exposed, a malicious actor may have been able to eavesdrop on private and encrypted communications.
GoDaddy has disclosed that they have taken steps to remediate the impact of the incident by resetting and issuing new credentials for both the default Administrator account as well as the sFTP and database access. The subset of customers with a compromised SSL private key has had new certificates issued and installed. It is important for affected customers to ensure that any compromised SSL certificates have been revoked.
RiskRecon provides the ability to assess your portfolio and determine whether you or any of your third parties may have been affected by this security incident. Once logged into your RiskRecon portal, you can navigate to the Data Search tab. For this particular security incident, we are interested in identifying “WordPress” Software whose Hosting Provider is “GoDaddy”.
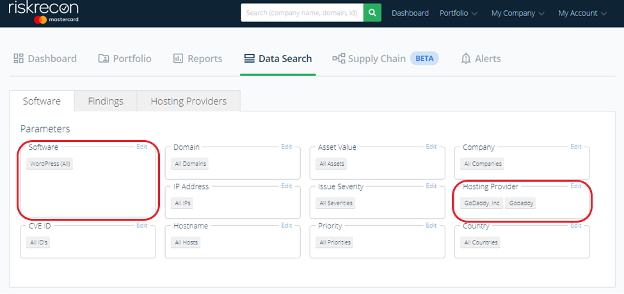
If you do not see any mention of either “WordPress” in your Software listing, or “GoDaddy” in your Hosting Provider listing, then RiskRecon has not identified either technology in your portfolio.
To learn more about RiskRecon’s platform and how you can get the most out of it, schedule a demo today.




