Many cybersecurity veterans will be quick to share the common wisdom that compliance does not equal effective cybersecurity risk management. But is there any truth behind this wisdom, or is it more of a symptom of the too often adversarial relationship between auditors and system administrators? Do compliance requirements lead to measurable benefits to risk management?
Cybersecurity regulations and frameworks, authored by a bevy of government and industry oversight groups, provide a barometer for baseline security best practices. Whether they’re coming from the PCI Council, NIST, ISO, or CIS, the requirements laid out by these compliance groups offer a reference point from which organizations can use to chart their security risk posture journey.
Checkbox compliance — the following of the bare minimum of compliance standards — surely isn’t a path leading to a robust risk management posture. At the same time, if we accept compliance risk (the threat of failing a mandated compliance regime and suffering adverse effects) as an element of an organization’s overall cyber risk, then it’s not unreasonable to suspect that a failure to manage this aspect of risk may well correlate with challenges in other parts of the risk profile.
While auditors may be the arbiters of how much headway an organization is making on its compliance-driven security improvements, relying solely on the auditor’s evaluations is a high-stakes, zero-sum game. Breaking down requirements into meaningful components and taking a progress-not- perfection approach can help facilitate meaningful continuous improvement both for cyber compliance and risk management. Stepping away from the proverbial mirror and getting a feel for how well an organization’s peers are complying with regulatory and framework standards can also provide some valuable insight
The big obstacle is that it can often be difficult to gauge how well an organization is performing compared to its peers. While some organizations may list the standards they follow, getting access to their performance through auditors’ reports is not generally possible. To that end, RiskRecon offers risk and compliance decision makers a peek under the covers to see how well the “other guys” are doing.
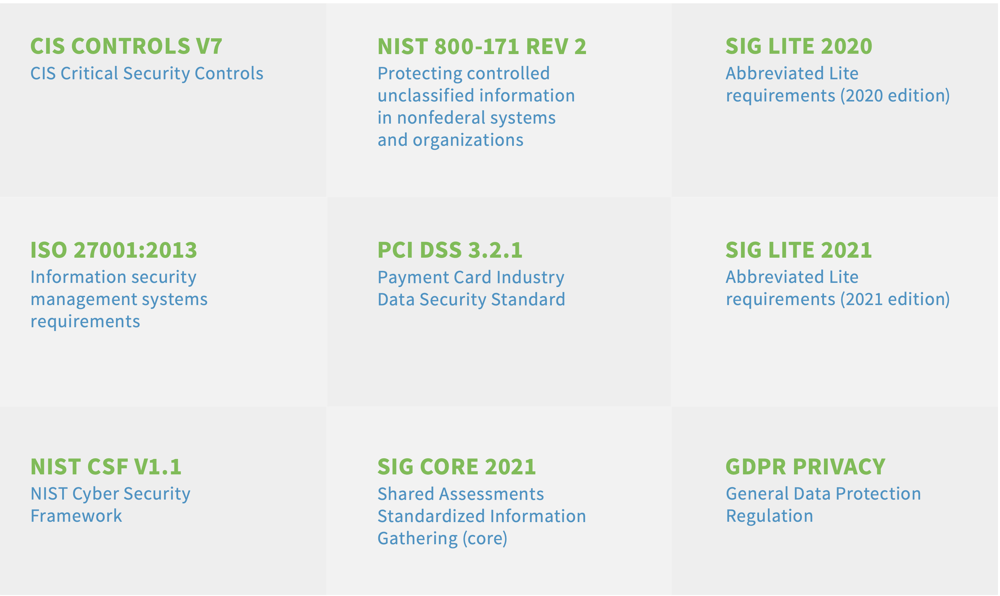
RiskRecon is able to offer this analysis based on findings from its cybersecurity ratings and assessment platform. This compliance report examines the security assessment results for tens of thousands of organizations around the world, and then mapping them to nine different modern cybersecurity compliance standards:
The mapping is fairly intuitive, since the checks done by RiskRecon’s third-party assessments cover many practices similar to those stipulated by the regulators. These include security requirements such as enabling email authentication, patching software and servers, and utilizing effective web encryption.
The caveat is that the data presented here is not as tightly scoped as an auditor’s assessment. While this is not a full audit of the tens of thousands of organizations in our dataset, we believe this to be a reasonable proxy to understand the types of issues organizations are struggling with. To help single out the things that matter the most, we focus on high value assets—which are also more likely to be in scope for audit findings. We recommend reading this report with the understanding that while this data isn’t an ironclad reading of compliance, it does offer reasonable indications of the nature of challenges that organizations today face in meeting compliance demands.







