Every organization faces information security threats. While most organizations are concerned with preventing data breaches, critical infrastructure operators face a much different threat landscape. These types of entities not only have to deal with preventing data loss but also preventing threat actors (commonly nation-states or APTs) from causing physical destruction.
 For example, parts of Ukraine’s power grid were shut down two Christmases in a row by an APT group known as Sandworm. In 2017, a piece of ransomware called NotPetya hit critical infrastructure (and other) organizations all over the world, causing ATMs, hospitals, postal services, and many other entities to shut down. By the time it stopped spreading, NotPetya is estimated to have caused $10 billion in damages worldwide.
For example, parts of Ukraine’s power grid were shut down two Christmases in a row by an APT group known as Sandworm. In 2017, a piece of ransomware called NotPetya hit critical infrastructure (and other) organizations all over the world, causing ATMs, hospitals, postal services, and many other entities to shut down. By the time it stopped spreading, NotPetya is estimated to have caused $10 billion in damages worldwide.
Additionally, many threats are targeting critical infrastructure; however, because of the sensitivity of these organizations’ offerings, many of these threats and incidents are not disclosed to the public.
To protect its citizens and economy from attacks against critical infrastructure, the European Union passed the Network and Information Systems (NIS) Directive. This Directive aims to ensure critical infrastructure operators, which include key internet enablers, can prevent, detect and respond to their unique threat landscape.
In this article, we talk about what NIS is and what your organization can do to comply with it.
Historical Context
One difference between European and American legislation, generally speaking, is that European legislation tends to be principles-based and American legislation tends to be very prescriptive. The same applies to NIS. Therefore, to understand the principles contained in NIS, it’s important to have a cursory understanding of how this directive came to be.
In 2013, the European Union (EU) created a formal cybersecurity plan to protect the open internet, online freedom and online opportunity for persons within the Union. The NIS Directive (EU 2016/1148) is the first EU-wide cybersecurity directive aimed at achieving the formal plan and was required to be transpositioned by Member States by 9 May 2018.
The “Critical Industries”
NIS considers 14 industries or, where applicable, the specific sub-industries to be in-scope. We list these below. Be aware, though, that if your organization operates in one of these industries, you may be subject to additional cybersecurity regulations imposed in each EU Member State. Be sure to consult with your organization’s legal counsel to ensure you’re complying with all applicable legislation.
- Energy
- Electricity
- Oil
- Gas
- Transportation
- Air transport
- Rail transport
- Water transport
- Road transport
- Banking
- Financial market infrastructures
- Healthcare
- Drinking water supply & distribution
- Digital infrastructure
- IXPs
- DNS service providers
- TLD name registries
NIS’s Main Requirements
The NIS directive has three main goals:
- Ensure each EU Member State has adequate cybersecurity capabilities (e.g., a national CERT, regular cyber exercises, etc.)
- Establish the NIS Cooperation Group, enabling collaboration, information sharing and coordination on implementing NIS between the EU Member States.
- Supervise the cybersecurity of critical industry operators.
While NIS leaves creating the specific cybersecurity requirements to each Member State, it does have specific requirements for reporting. Under these reporting requirements, an organization’s third-party digital service providers (i.e., any entity that provides a digital service) must notify the organization of any cybersecurity incident that significantly impacts the organization’s essential services. Because of this, and the general risk third-parties entail, organizations need to manage their third-party risk.
Notification Requirements
Similar to GDPR’s notification requirements, an organization’s third-party digital service providers must notify the organization of any cybersecurity incident that significantly impacts the organization’s essential services. Unlike GDPR, though, is that the term “incident” involves much more than data breaches involving personal information.
Under NIS, an incident is “any event having an actual adverse effect on the security of network and information systems.” If an organization’s digital service providers, suffers an incident, they must report it without undue delay to the appropriate Member State’s competent authority or CSIRT (i.e., CERT). The purpose of these notifications to CSIRTs is to ensure the incident is appropriately resolved. The CSIRT will then, in coordination with other Member States’ CSIRT if needed, assess the digital service provider’s security & commercial interests and decide if the public needs to be informed.
Third-party Risk Management
The NIS Directive is intended to assist operators of critical infrastructure in creating cybersecurity programs that can appropriately prevent, detect, notify authorities of and respond to security incidents. Part of this includes managing third parties’ security risks.
Third-party risk management is important for every organization; however, it’s vital for critical infrastructure operators. Critical infrastructure is consistently targeted by nation-states, and they are (generally) very patient, very skilled and highly motivated. This means that nation-states pose a much greater threat than your typical cybercriminal.
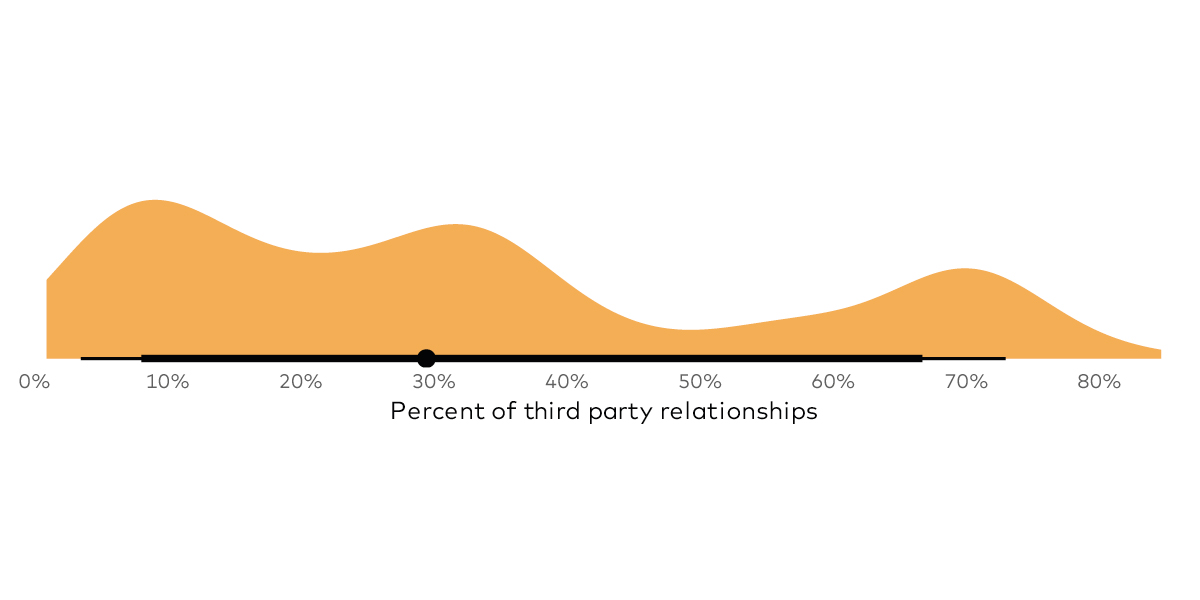
When organizations outsource, they lose direct control of their security posture. It’s imperative, then, for organizations to appropriately manage their third-parties. Most organizations have dozens, if not hundreds of vendors. Traditionally, managing these vendors has been done through questionnaires, spreadsheets and occasionally audits. These only provide a point-in-time, often a self-reported analysis of a vendor’s security posture.
RiskRecon addresses these issues by providing real-time, independent verification of how vendors are performing. This enables organizations to address their vendors’ risks in real-time, rather than waiting until next year’s reassessment.