Amazon Web Services provides a mind-boggling expanse of systems, services, and applications. An all-encompassing AWS security assessment guide would fill hundreds of pages. Rather than chew it all at once, our new AWS Core Security Assessment Playbook covers the essential foundations on which an AWS environment is built. Each of the 33 AWS Core Security Criteria featured in our new toolkit was carefully selected based on its necessity to ensuring a secure AWS environment. In this blog, we will introduce the six security domains in the playbook and why these are critical for proper AWS security configurations.
 The AWS Core Security Criteria covers six security domains:
The AWS Core Security Criteria covers six security domains:
- AWS Account Management
- Encryption
- Identity and Access Management
- Network Security
- Detection and Monitoring
- Processes
AWS Account Management
What is it? The AWS accounts and associated configurations structurally separate the various AWS environments (prod, staging, dev) to achieve effective separation of systems and user responsibilities. Access to the Root is protected using two-factor authentication and it is used only when no other options are available.
Why is it important? All aspects of AWS are controlled through administrative console-based configuration. Using accounts and related permissions to structurally segment the various environments and responsibilities helps ensure proper control and configuration.
Encryption
What is it? AWS data store encryption features are implemented to encrypt data at rest.
Why is it important? The use of the AWS data store encryption feature helps prevent a breach of data in the event of physical storage media theft or improper hardware redeployment or retirement.
Identity and Access Management
What is it? The AWS environment is supported by a robust identity and access management infrastructure. Sensitive permissions are properly managed to ensure appropriate use. Programmatic access is strictly controlled.
Why is it important? A well-configured AWS identity and access management infrastructure helps ensure that all user access is appropriate and authorized, minimizing the likelihood of privilege abuse or error.
Network Security
What is it? The AWS network is segmented into subnets according to required system network access requirements. Network services are limited to those that are secure and necessary. Internet-facing services are restricted to least privilege, exposing only those necessary for the given user population.
Why is it important? Segmenting systems into different subnets, such as public and internal, helps ensure that internal-only systems aren’t accidentally exposed. Limiting network services to only those users who absolutely must access them reduces the likelihood of compromise.
Detection and Monitoring
What is it? The AWS Config service is enabled across the implementation and configured to inventory and report the configuration of all AWS assets. All systems are authorized and configured to security standards. Security event monitoring services are implemented and monitored.
Why is it important? Maintaining current knowledge of all assets and their configuration is essential to achieving good risk outcomes; you can’t protect what you don’t know exists or what you don’t understand. Monitoring the environment for security events enables you to limit the impact of errors and incidents.
Processes
What is it? Methodologies and tools are used to reliably maintain the security of the environment.
Why is it important? Maintaining the security of the AWS environment using well-established methodologies and tools helps ensure that desired outcomes are consistently achieved.
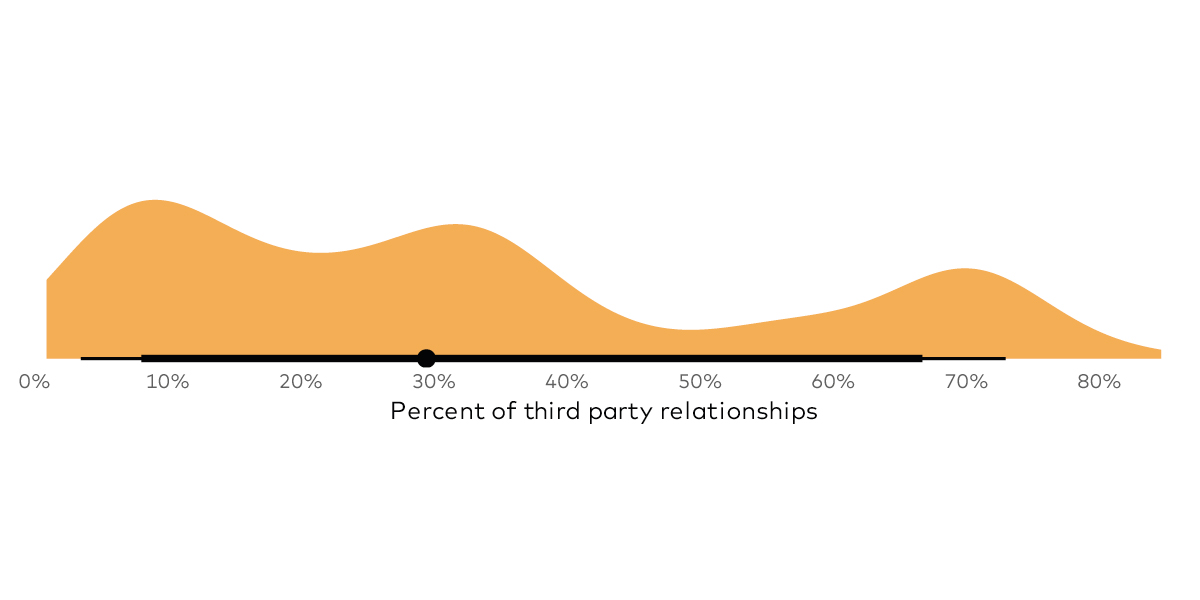
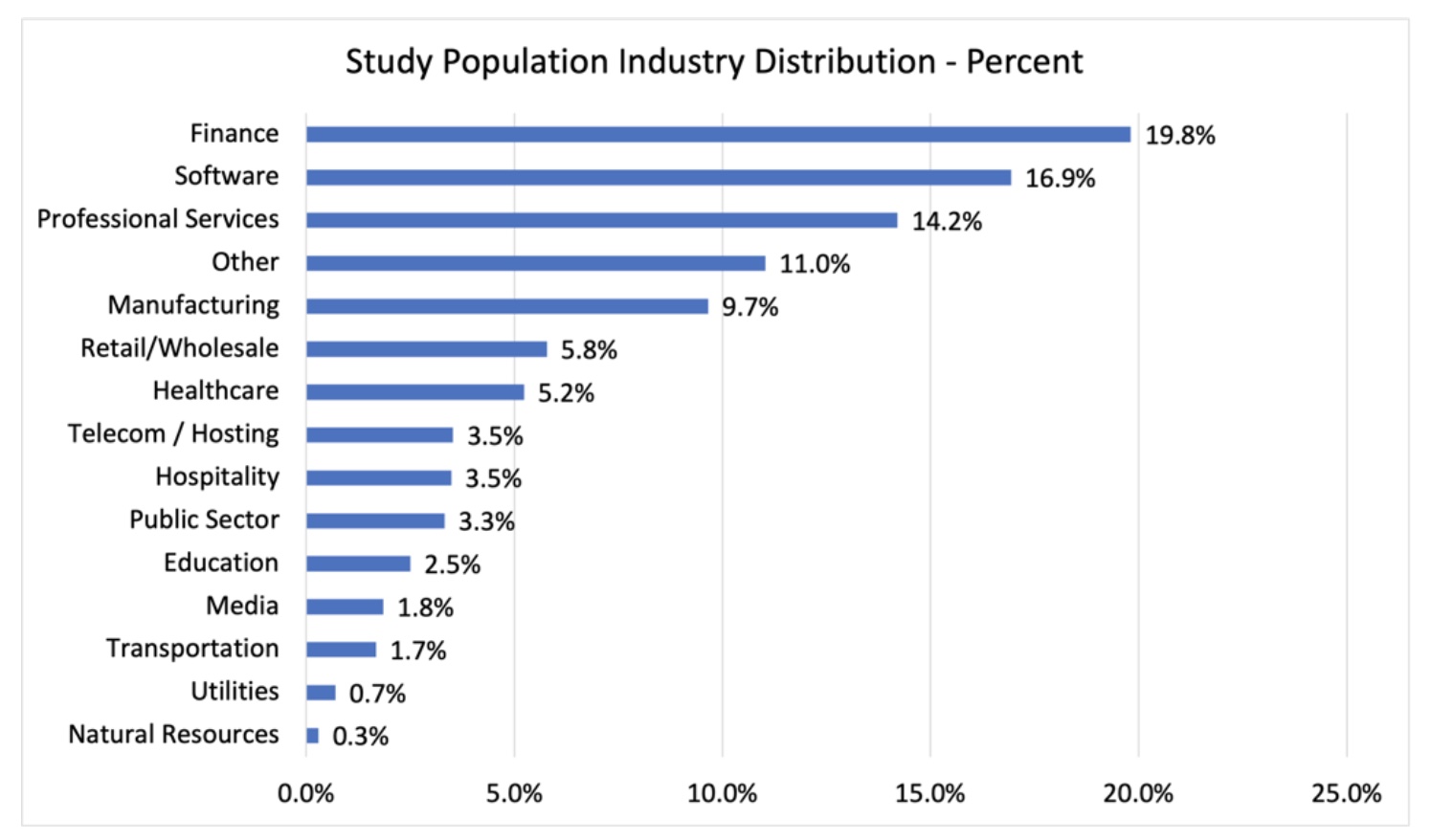
As organizations of all shapes and sizes increase their reliability on vendors they rarely see or touch, it is of vital importance that proper vetting is done to ensure your critical data is secured. AWS is the most widely used cloud service on the planet, so chances are high that someone you are working with is utilizing the platform in some fashion. Using our AWS Assessment Questionnaire, built on the security domains mentioned above, will allow you to gain a better understanding of how any third-party is operating in AWS and will measure the security of those configurations. Don't get caught assuming that an AWS deployment is secure, we all know how that story can go.