Let’s take a look at the kinds of organizations most likely to be involved in a ripple event, including the generating organizations, recipients of downstream loss events, and threat actors.
THE VICTIMS
As with last year’s report, we leaned on the North American Industry Classification System (NAICS) for this analysis. NAICS is widely used, well-documented, and conveniently integrated into Advisen’s cyber loss database. This year, we started with the work performed by our partners at Advisen in identifying the generating sources of ripples and completed additional research on a large portion of the ripple events.
In doing so, we were able to more precisely identify the source of ripple events than in the last edition of this report. While we’re confident in our determinations, putting the numbers from each report side by side does lead to an apples-and-oranges comparison. Instead, we focus on the picture of where things stand in the overall dataset, keeping in mind that this covers a 10-year period.
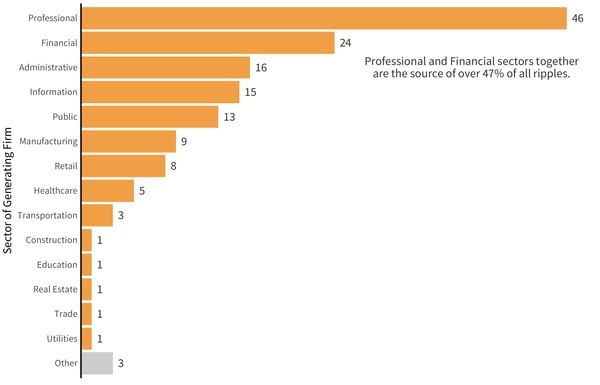
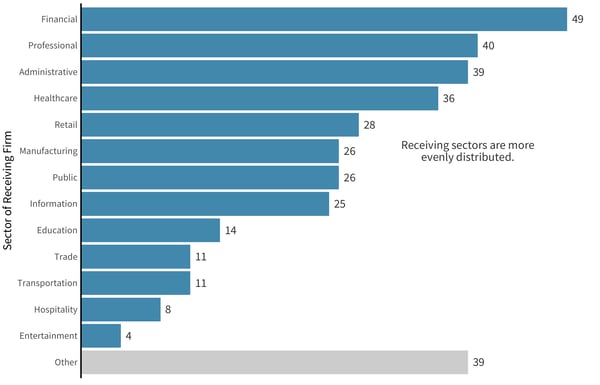
Most Common Industries as Generators and Receivers
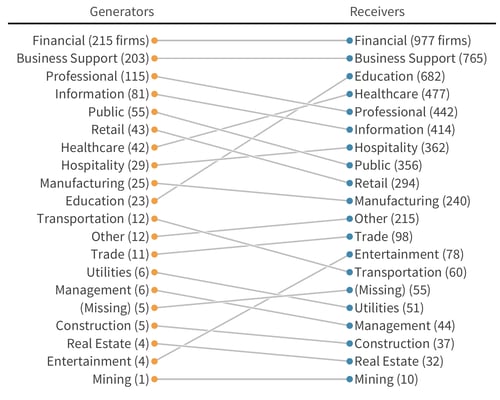
As you can see in figure above, comparing ripple-generating victims against recipients of downstream loss events, financial and business support organizations dominate the top two slots in both categories. One of the lessons we want to convey with this comparison chart is that there are a lot of crossovers between the generators and receivers. Many companies are, at some point, both the generator of one ripple event and the downstream recipient of others generated by different organizations. This is a testament to the tight technical ties that bind suppliers, customers, and partners in today’s digitally dominated business environment.
By comparing generators (orange) and receivers (blue), we also examined our ripple victims by company size. The data below is made up of a subset of companies for which we had employee data available, which accounts for about 89% of all companies involved.
Employee Data for Companies Involved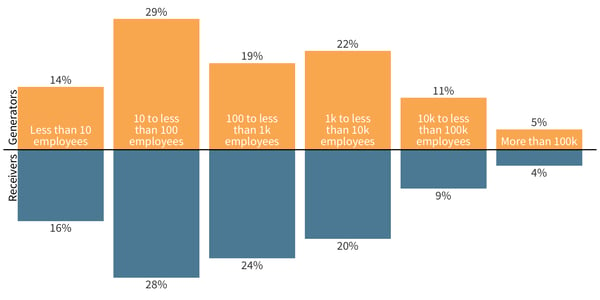
One thing of note here is that the generators (orange) are much more oriented toward smaller firms than the balance we saw in 2019. In contrast, a fairly constant balance remained between the larger and smaller receiving firms. Similar to our breakdown by industry, the ratios by the number of employees between the two groups seem nearly symmetrical, indicating that the company size doesn’t make firms any more or less likely to be a ripple generator or receiver.
Among the newly observed ripples, generating organizations saw a surge among the professional industry in particular, even if the overall data set showed financials led the way. Meanwhile, downstream organizations in the newly observed ripples more closely matched the existing ratios, with financial services firms and professional organizations coming in first and second, respectively.
Generating Sectors with New Ripples
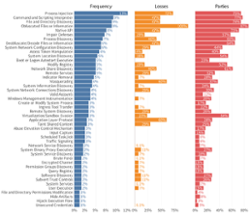
THE THREAT ACTORS
The threat actors who trigger ripple breach events can be difficult to trace. Here, we present the data from events for which we have information about the primary actors involved. Ripples can have multiple “primary” parties, so a single ripple may appear in several of the following bars.
Threat Actors Involved with Ripples
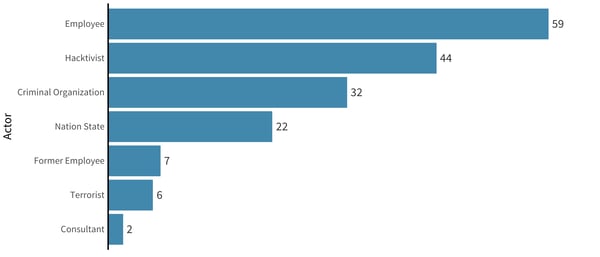
We’ve removed the ripple events wherein the actor is a trusted third-party vendor. All of these ripples are third-party types by nature, as we’re looking to understand the events associated with the ultimate genesis of a ripple. We have also removed the “Organization” actor type; this often represents one firm suing another (or regulatory action), and we’re looking for the ultimate source of ripples.
Download the report now to see the full analysis.